Patient Data Encryption Tool
- Project Started: February 2015
- Last Worked on Version: 2.0.2
- Releases: 2 Major Versions
- Node.js
- Node Webkit
- OpenSSL
- Node.js Crypto API
About
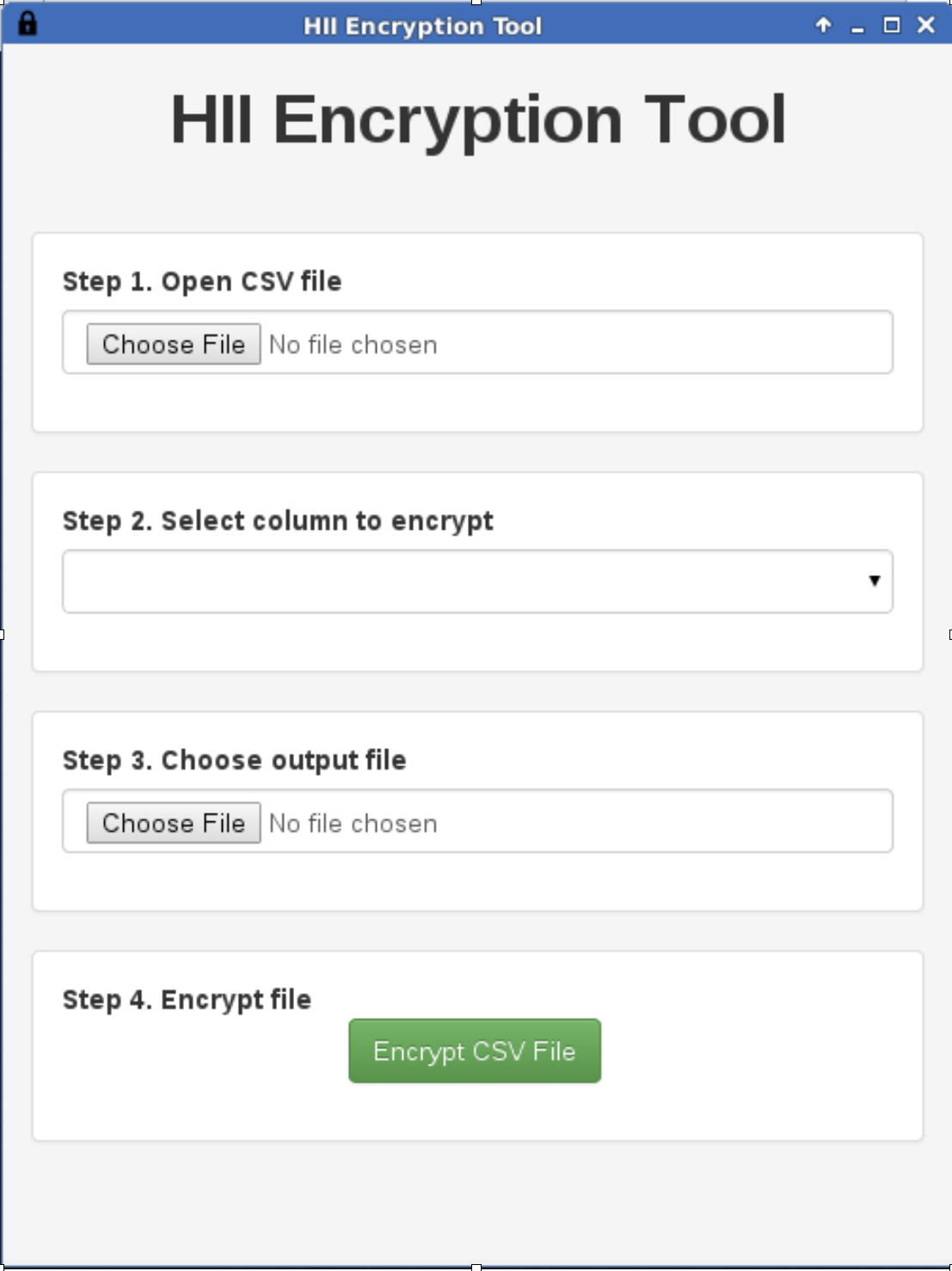
As part of a larger HSE Project, I was required to build a tool that could selectivity encrypt a single column of data in a CSV file such as full name, postal address or medical reference number (MRN). The encrypted data would also need to be decrypted upon request within a web browser if a valid private key was provided. This presented a number of challenges in terms of the tool design and future decryption which would be required to run on older HSE hardware. The data to be processed was PAS (Patient Administration Data) from each of the hospitals in Ireland. CSV files could easily exceed millions of rows for multiple years and various report and export tools used in each hospital did not follow the CSV standard exactly.
With all these requirements in mind, I developed a Node Webkit based application which used streams and the crypto APIs to facilitate the encryption
Encryption Methodology
Firstly, a user must select a CSV file with at least one column of data to encrypt. The tool then generates two cryptographically strong pseudo-random strings of 128 bits each. Both strings are then processed by a 2nd generation Password-Based Key Derivation Function to make a unique encryption key for this session (known as the session encryption key). It is important to note that this key will change every time the tool is run. The chosen column of data is then encrypted with the session encryption key and the XXTEA (Corrected Block TEA) cipher algorithm at 128 bits. The XXTEA cipher was chosen due to its speed and ability to run in a web browser for later decryption.
The session encryption key is then RSA encrypted using a known public key ( 1024 bits ) and is appended to each row of encrypted data. This allows for decryption at a later date as the unique session encryption key follows the encrypted rows. The CSV data is then saved to the users computer for inspection.
Key Management
To control access to individual hospital records, a system of key management was implemented. A master key pair was generated and entrusted to the client (HSE). This master public key is used by the encryption tool for protecting data.
The data is used consumed by a web based reporting and analysis system which forms part of Health Atlas Ireland. To allow end users access patient data at a later stage within this system, each is provided with their own unique authentication bundle which is associated with their account. The bundle contains a copy of the private master key and additional attributes such as hospital group, UUID and expiry date. A user must supply the correct password to decrypt a given set of records.
To further enhance security, a user must also be present in the hospital for which the records are associated. This is enforced by matching IP addresses with a database of approved access locations. Users must also have an account on the system with the appropriate privilege and roles.
Web Decryption
When a user requests decryption of a given set of records, a number of checks on location and privileges are made before releasing the encrypted bundle to the web browser. The user is then prompted for their unique password to decrypt the required key and metadata. The XXTEA algorithm is used for both encryption and decryption of the bundle and assuming decryption was successful, a JSON object should be decoded.
The private key string is then used to RSA decrypt the session key used by each record. Records containing the same encrypted session key string are grouped and decrypted once as RSA decryption is expensive, even in modern browsers. Once the session key is available, each record is XXTEA decrypted and available for display to the user.
It is important to note that this decryption process is cairned out entirely within the users web browser and no information is shared over the web in clear text format. The information remains in memory only for the duration of the session and is deleted afterwards.